-
Private chats and photos of celebrities and influencers were exposed after a suspected stalkerware setup left a database open, revealing sensitive messages and files.
¶¶¶¶¶
¶¶¶¶¶
¶¶¶¶¶
¶¶¶¶¶
¶¶¶¶¶
-
The Marine Corps has long insisted that it needs enough amphibious ships to keep three ready groups deployed at all times, but the demand for those units is much higher than that, the service’s commandant said Thursday.
Every combatant commander—from U.S. Central Command to Africa to Southern—has requested an ARG with a Marine Expeditionary Unit on board, Gen. Eric Smith told an audience at the Modern Day Marine conference in Washington, D.C.
“I won't say how many of the ARG-MEUs our combat commanders ask for, but it is well north of three,” he said. “I'll just say that it is well north of three—like double that.”
The 22nd MEU is off the coast of South America supporting Operation Southern Spear, the administration’s anti-drug trafficking effort, while the 31st MEU is in the Middle East supporting the U.S. blockade of Iran.
They’ll soon be joined by the 11th MEU, Smith said, which just finished typhoon disaster response in the Northern Mariana Islands.
“I just wish I had more of them to offer,” he said.
Having an ARG-MEU constantly off both coasts of the U.S. and in the Indo-Pacific is the goal, and while the Corps has the Marines to do it, it does not have the ships.
Out of the Navy’s 32 amphibious ships, only about half are in good enough condition to keep deploying, according to a 2024 Government Accountability Office report. The Navy would need to have nine in deployable condition at any given time to get to the 3.0 presence the commandant wants, with the rest in various stages of maintenance and pre-deployment training in order to keep the pipeline primed.
The service needs more like 40 to support the effort, Lt. Gen. Jay Bargeron, deputy commandant for plans, policies, and operations, said during a presentation Wednesday at Modern Day Marine, but an ongoing analysis is working on a precise number. By law, the Navy has to have 31, but the law doesn’t govern whether they are deployable.
“The Navy and the Marine Corps are aligned on this: 31 is not the right number,” Bargeron said. “It’s a floor, as was described.”
The Navy is working on building more amphibs, while also tackling the problem of delayed and backlogged maintenance to its existing fleet with the Amphibious Force Readiness Board.
“Its purpose is simple: to increase operational availability, to reduce maintenance delays, to prioritize modernization that actually improves readiness, to improve accountability across the enterprise, better synchronize daily Marine Corps demand signals, and last, generate more usable presence from the force we already have,” Adm. Daryl Caudle, the chief of naval operations, said Thursday at Modern Day Marine.
Caudle said he is encouraged by some of the maintenance that West Coast ships have been able to fast-track, and acknowledged that the East Coast is making a similar effort.
“But we are not declaring victory early,” he added. “This will take sustained pressure and leadership from the Pentagon to the commanding officers on the waterfront.”
]]>¶¶¶¶¶
¶¶¶¶¶
¶¶¶¶¶
¶¶¶¶¶
¶¶¶¶¶
-
It’s been two months since the U.S. began strikes on Iran without authorization from Congress, so the clock is about to run out on the legal amount of time a president has to carry out a military operation without congressional approval. But the administration has given no indications they hope to make Operation Epic Fury legal.
Asked during a Senate Armed Services Committee hearing Thursday whether an authorization or extension request are coming, Defense Secretary Pete Hegseth demurred, arguing that the current ceasefire with Iran has paused the 30-day clock.
“I do not believe the statute supports that,” Sen. Tim Kaine, D-Va., told Hegseth. “We have serious constitutional concerns and we don’t want to layer those with additional statutory concerns.”
A White House spokeswoman did not respond to a request from Defense One to clarify whether the president has asked Congress to vote on an authorization for use of force in Iran, or whether he will submit a written request for a 30-day extension that would give troops time to withdraw.
One or the other is required to extend a military operation past 60 days, per the War Powers Resolution of 1973.
“The current ceasefire does not affect the clock,” David Janovsky, acting director of the Constitution Project at the Project on Government Oversight, said in a statement Thursday. “The War Powers Resolution is written in very broad terms. It refers to ‘hostilities,’ not ‘war,’ and it even covers situations where hostilities are imminent but not actually occurring.”
Though the ceasefire began April 8, the U.S. has since instituted a blockade against Iran, Janovsky said, “an act of war in its own right, and one that has included U.S. troops boarding multiple Iranian ships.”
“And yet, Secretary Hegseth, you declared victory a month ago,” SASC ranking member Sen. Jack Reed, D-R.I., said during Thursday’s hearing. “On April 8, you said, ‘Operation Epic Fury was a historic and overwhelming victory … By any measure, Epic Fury decimated Iran’s military and rendered it combat ineffective for years to come.’ “
Republican lawmakers have blocked multiple attempts by Democrats to hold a war powers vote. Senate Democrats on Thursday announced they would force an initial same-day vote, though a final vote wouldn’t be scheduled until Friday, despite the 60-day clock running out Thursday night.
]]>¶¶¶¶¶
¶¶¶¶¶
¶¶¶¶¶
¶¶¶¶¶
¶¶¶¶¶
-
Replacing the dozens of U.S. aircraft that have been damaged or destroyed in the Iran war will require more money than the staggering $1.5 trillion defense budget, the Air Force’s top general said.
Air Force Gen. Kenneth Wilsbach, the service’s top uniformed leader, told House lawmakers Thursday that the historic defense budget is focused on buying more fighters, bombers, and tankers for the service’s fleet. Those losses in Iran have made additional funding from Congress outside the 13-figure budget request necessary, he said during a defense appropriations subcommittee hearing.
“We hope to be able to address this in a supplemental, for the aircraft that we’ve lost, and the procurement, going forward, is meant to increase the number of tails we have, especially in the fighter force, but it also includes bombers and tankers as well,” Wilsbach said. “Both supplemental and the budget, the ‘27 budget, is supposed to address those losses.”
Key U.S. Air Force assets, including a $500 million E-3 Sentry and four F-15E fighter jets, have been lost since Operation Epic Fury began in late February. Overall, nearly 40 U.S. aircraft have been destroyed and roughly 10 have been damaged, according to The War Zone’s tally of open-source information. Jules W. Hurst III, who is performing the duties of the Pentagon comptroller and chief financial officer, told reporters earlier this month that the $1.5 trillion budget, consisting of yet-to-be-approved reconciliation funds, was formulated “before we went into conflict with Iran.”
Hurst told House lawmakers Wednesday that the Defense Department has spent an estimated $25 billion during the two months of Iran war operations—a figure is reportedly much higher when accounting for base and aircraft damage. Rep. Ro Khanna, D-Calif, said during the hearing that figure appeared to be “totally off.”
The administration has been seeking anywhere from $98 billion to more than $200 billion in supplemental funding for the ongoing war in Iran.
But Rep. Ken Calvert, the defense appropriations subcommittee chairman, told Air and Space Force leaders during the opening of Thursday’s hearing that lawmakers haven’t gotten details on an Iran war supplemental yet.
“I also want to acknowledge the aircraft we’ve lost and munitions we’ve expended in Iran, which is not insignificant,” the California Republican said. “We may see a request for a supplemental at some point, but we have not seen it yet. And it’s unclear how we plan to replenish stocks and address losses we’ve taken in our Air Force inventory.”
A supplemental would require more Congressional buy-in and oversight, versus additional reconciliation spending, which would be approved by a simple majority. While the Trump administration relied heavily on reconciliation funding for last year’s defense priorities, top lawmakers have said it’s not a certainty this year.
Rep. Betty McCollum, D-Minn., said supplemental funding is preferred to reconciliation funds for the Air Force’s priorities because it can also be more easily accounted for, which has been a concern for lawmakers after the passage of Trump’s One Big Beautiful Bill Act.
“We have no idea what is going to be happening in future base budgets,” said McCollum, the ranking member of the defense appropriation subcommittee. “That's why having things built into the base or in a supplemental where we can track and know how the money is going to happen, versus a reconciliation, is so very important.”
]]>¶¶¶¶¶
¶¶¶¶¶
¶¶¶¶¶
¶¶¶¶¶
¶¶¶¶¶
-
A misconfigured server linked to the carding marketplace Jerry’s Store exposed 345,000 stolen credit cards after an AI coding error caused a major security flaw.
¶¶¶¶¶
¶¶¶¶¶
¶¶¶¶¶
¶¶¶¶¶
¶¶¶¶¶
-
In yet another software supply chain attack, threat actors have managed to compromise the popular Python package Lightning to push two malicious versions to conduct credential theft. According to Aikido Security, Socket, and StepSecurity, the two malicious versions are versions 2.6.2 and 2.6.3, both of which were published on April 30, 2026. The campaign is assessed to be an extension of the
¶¶¶¶¶
¶¶¶¶¶
¶¶¶¶¶
¶¶¶¶¶
¶¶¶¶¶
-
·
Apex wants to provide satellite buses to primes building proliferated constellations, which means building at scale, CEO Ian Cinnamon says.The company recently announced plans to make an XL version of its Comet satellite bus, adding power and mass yet still remaining small enough to fit 16 on a Falcon 9, Apex CEO Ian Cinnamon said in a recent interview.
But, he said, “I think what everybody tends to forget about is the need to really build these at really high rate production. And that's really the focus around Comet.”
Cinnamon said Apex builds at scale by reusing avionics and other systems from its earlier, medium-sized Nova bus—but also by using Octopus, the custom software that he calls his company’s “secret sauce.”
“Effectively, it's not even our manufacturing operating system; it's our entire company operating system,” he said. “It controls everything from, you know, forecasting demand, understanding on inventory, receiving quality from suppliers. How many, you know, kits we're holding on inventory at any given time, all the way to work, instructions on the factory floor, tracking, NCRs, traceability on orbit.”
Like seemingly everything else these days, Octopus “uses a significant amount of artificial intelligence, a significant amount of software automation for processes,” the CEO said.
But what Apex doesn’t use—at least not yet—is industrial robotics.
“We do not believe that automation and robots, in terms of the hardware manufacturing, makes sense at all at the scale that we're building,” he said. “It does not make sense at the scale of hundreds of vehicles per year…When you go above that scale, it may begin to make sense.”
Welcome
You’ve reached the Defense Business Brief, where we dig into what the Pentagon buys, who they’re buying from, and why. Send along your tips, feedback, and song recommendations to lwilliams@defenseone.com. Check out the Defense Business Brief archive here, and tell your friends to subscribe!
A new ad is pushing Congress to fund American shipbuilding to combat China and its growing commercial and naval fleets—and also increase jobs and domestic manufacturing. The USA Shipbuilding Coalition, composed of shipbuilders and unions, released the video Wednesday—with timing that appears to coincide with SHIPS Act legislation challenges.
- The ad, which targets national streaming platforms and local TV markets in Louisiana, Mississippi, and Texas, highlights the decades-long decline in American shipbuilding capacity as China’s has increased, something the second Trump administration has focused on.
- “We cannot out-China the Chinese, competing in a system they have bent to their advantage.
- We need to alter the terms of competition and that means beginning where maritime strength begins, cargo. It means using public policy to create the conditions for predictable demand, fleet formation, shipyard investment and workforce continuity,” Capt. Stephen Carmel, maritime administrator for the Transportation Department told Congress last week.
- “Without cargo, there is no requirement for ship construction, no vessel deployments, no utilization of port infrastructure, and no operating environment within which maritime services can occur,” he said in written testimony.
Defense tech startup Firestorm Labs snags $82 million in its Series B funding round led by Washington Harbour Partners, which said the company is “building a new model for manufacturing.” The new capital will help Firestorm increase production of its mobile 3D-printing xCell platform that can be set up in a matter of hours, manufacturing everything from drones to prosthetics to tools.
- Background: The company announced a $100 million deal with the Air Force for additive manufactured drones earlier this year and boasts a $153 million total investment counting this latest funding round.
- Just a thought: What’s interesting is the idea of bringing digital-based one stop manufacturing shops that could help troops fill basic needs, like printing knee braces instead of ordering them, in tactical environments. I wonder if these platforms could make an appearance in an upcoming military exercise…
One more manufacturing thing: Pentagon-funded institution BioMADE is putting up $21.4 million to expand domestic biomanufacturing. The funds will support 14 projects in areas like biosensors to help detect disease, plastics used for 3D printing, and proteins for wound healing and chemical defenses.
]]>¶¶¶¶¶
¶¶¶¶¶
¶¶¶¶¶
¶¶¶¶¶
¶¶¶¶¶
-
As more businesses relocate their operations to the cloud, one important decision arises: should you choose managed or…
¶¶¶¶¶
¶¶¶¶¶
¶¶¶¶¶
¶¶¶¶¶
¶¶¶¶¶
-
A Brazilian tech firm that specializes in protecting networks from distributed denial-of-service (DDoS) attacks has been enabling a botnet responsible for an extended campaign of massive DDoS attacks against other network operators in Brazil, KrebsOnSecurity has learned. The firm’s chief executive says the malicious activity resulted from a security breach and was likely the work of a competitor trying to tarnish his company’s public image.

An Archer AX21 router from TP-Link. Image: tp-link.com.
For the past several years, security experts have tracked a series of massive DDoS attacks originating from Brazil and solely targeting Brazilian ISPs. Until recently, it was less than clear who or what was behind these digital sieges. That changed earlier this month when a trusted source who asked to remain anonymous shared a curious file archive that was exposed in an open directory online.
The exposed archive contained several Portuguese-language malicious programs written in Python. It also included the private SSH authentication keys belonging to the CEO of Huge Networks, a Brazilian ISP that primarily offers DDoS protection to other Brazilian network operators.
Founded in Miami, Fla. in 2014, Huge Networks’s operations are centered in Brazil. The company originated from protecting game servers against DDoS attacks and evolved into an ISP-focused DDoS mitigation provider. It does not appear in any public abuse complaints and is not associated with any known DDoS-for-hire services.
Nevertheless, the exposed archive shows that a Brazil-based threat actor maintained root access to Huge Networks infrastructure and built a powerful DDoS botnet by routinely mass-scanning the Internet for insecure Internet routers and unmanaged domain name system (DNS) servers on the Web that could be enlisted in attacks.
DNS is what allows Internet users to reach websites by typing familiar domain names instead of the associated IP addresses. Ideally, DNS servers only provide answers to machines within a trusted domain. But so-called “DNS reflection” attacks rely on DNS servers that are (mis)configured to accept queries from anywhere on the Web. Attackers can send spoofed DNS queries to these servers so that the request appears to come from the target’s network. That way, when the DNS servers respond, they reply to the spoofed (targeted) address.
By taking advantage of an extension to the DNS protocol that enables large DNS messages, botmasters can dramatically boost the size and impact of a reflection attack — crafting DNS queries so that the responses are much bigger than the requests. For example, an attacker could compose a DNS request of less than 100 bytes, prompting a response that is 60-70 times as large. This amplification effect is especially pronounced when the perpetrators can query many DNS servers with these spoofed requests from tens of thousands of compromised devices simultaneously.
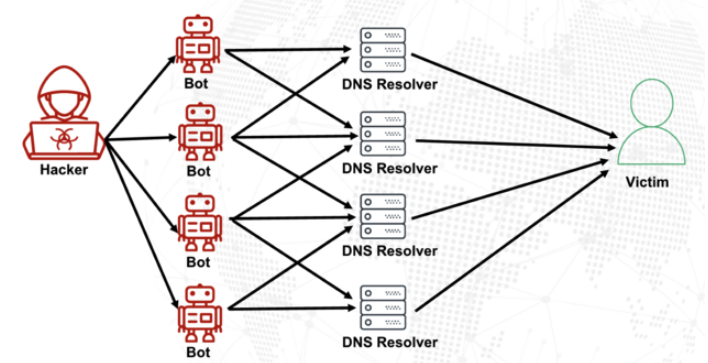
A DNS amplification and reflection attack, illustrated. Image: veracara.digicert.com.
The exposed file archive includes a command-line history showing exactly how this attacker built and maintained a powerful botnet by scouring the Internet for TP-Link Archer AX21 routers. Specifically, the botnet seeks out TP-Link devices that remain vulnerable to CVE-2023-1389, an unauthenticated command injection vulnerability that was patched back in April 2023.
Malicious domains in the exposed Python attack scripts included DNS lookups for hikylover[.]st, and c.loyaltyservices[.]lol, both domains that have been flagged in the past year as control servers for an Internet of Things (IoT) botnet powered by a Mirai malware variant.
The leaked archive shows the botmaster coordinated their scanning from a Digital Ocean server that has been flagged for abusive activity hundreds of times in the past year. The Python scripts invoke multiple Internet addresses assigned to Huge Networks that were used to identify targets and execute DDoS campaigns. The attacks were strictly limited to Brazilian IP address ranges, and the scripts show that each selected IP address prefix was attacked for 10-60 seconds with four parallel processes per host before the botnet moved on to the next target.
The archive also shows these malicious Python scripts relied on private SSH keys belonging to Huge Networks’s CEO, Erick Nascimento. Reached for comment about the files, Mr. Nascimento said he did not write the attack programs and that he didn’t realize the extent of the DDoS campaigns until contacted by KrebsOnSecurity.
“We received and notified many Tier 1 upstreams regarding very very large DDoS attacks against small ISPs,” Nascimento said. “We didn’t dig deep enough at the time, and what you sent makes that clear.”
Nascimento said the unauthorized activity is likely related to a digital intrusion first detected in January 2026 that compromised two of the company’s development servers, as well as his personal SSH keys. But he said there’s no evidence those keys were used after January.
“We notified the team in writing the same day, wiped the boxes, and rotated keys,” Nascimento said, sharing a screenshot of a January 11 notification from Digital Ocean. “All documented internally.”
Mr. Nascimento said Huge Networks has since engaged a third-party network forensics firm to investigate further.
“Our working assessment so far is that this all started with a single internal compromise — one pivot point that gave the attacker downstream access to some resources, including a legacy personal droplet of mine,” he wrote.
“The compromise happened through a bastion/jump server that several people had access to,” Nascimento continued. “Digital Ocean flagged the droplet on January 11 — compromised due to a leaked SSH key, in their wording — I was traveling at the time and addressed it on return. That droplet was deprecated and destroyed, and it was never part of Huge Networks infrastructure.”
The malicious software that powers the botnet of TP-Link devices used in the DDoS attacks on Brazilian ISPs is based on Mirai, a malware strain that made its public debut in September 2016 by launching a then record-smashing DDoS attack that kept this website offline for four days. In January 2017, KrebsOnSecurity identified the Mirai authors as the co-owners of a DDoS mitigation firm that was using the botnet to attack gaming servers and scare up new clients.
In May 2025, KrebsOnSecurity was hit by another Mirai-based DDoS that Google called the largest attack it had ever mitigated. That report implicated a 20-something Brazilian man who was running a DDoS mitigation company as well as several DDoS-for-hire services that have since been seized by the FBI.
Nascimento flatly denied being involved in DDoS attacks against Brazilian operators to generate business for his company’s services.
“We don’t run DDoS attacks against Brazilian operators to sell protection,” Nascimento wrote in response to questions. “Our sales model is mostly inbound and through channel integrator, distributors, partners — not active prospecting based on market incidents. The targets in the scripts you received are small regional providers, the vast majority of which are neither in our customer base nor in our commercial pipeline — a fact verifiable through public sources like QRator.”
Nascimento maintains he has “strong evidence stored on the blockchain” that this was all done by a competitor. As for who that competitor might be, the CEO wouldn’t say.
“I would love to share this with you, but it could not be published as it would lose the surprise factor against my dishonest competitor,” he explained. “Coincidentally or not, your contact happened a week before an important event – one that this competitor has NEVER participated in (and it’s a traditional event in the sector). And this year, they will be participating. Strange, isn’t it?”
Strange indeed.
¶¶¶¶¶
¶¶¶¶¶
¶¶¶¶¶
¶¶¶¶¶
¶¶¶¶¶
-
The internet is noisy this week. We are seeing some wild new tactics, like people using fake cell towers to send scam texts, while some developers are accidentally downloading tools that peek into their private files during a simple install. It is definitely a busy time to be online. Security is always a moving target. Millions of servers are currently sitting online without any passwords, and
¶¶¶¶¶
¶¶¶¶¶
¶¶¶¶¶
¶¶¶¶¶
¶¶¶¶¶


